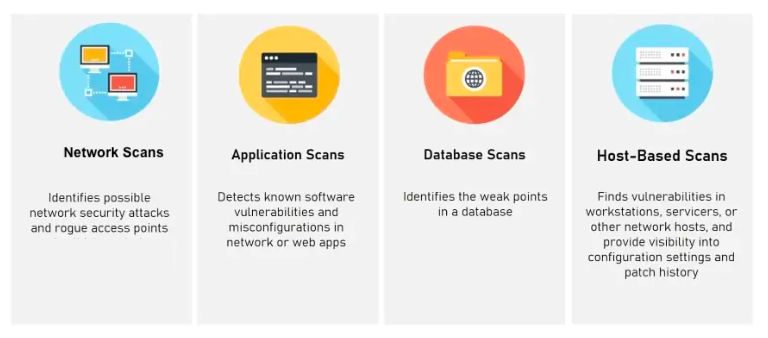
Vulnerability scanning is a crucial component of the security assessment process, aimed at identifying potential vulnerabilities in various aspects of an organization’s infrastructure. It involves using automated tools to scan networks, applications, databases, and host systems for known security weaknesses and misconfiguration.
Network Scan
Network scanning involves the systematic scanning of a network infrastructure to identify vulnerabilities in a network. The scanning tools perform various checks and tests to detect open ports, outdated firmware, misconfigurations, weak protocols, and other potential vulnerabilities. The goal is to identify areas where an attacker could gain unauthorized access or launch network-based attacks. Network scanning helps organizations ensure that their network infrastructure is properly secured, and appropriate security measures, such as firewalls and access controls, are in place.
Application Scan
Application scanning focuses on identifying vulnerabilities in web applications, mobile applications, or other software applications. It involves testing the application for common security flaws, such as injection attacks, cross-site scripting (XSS), insecure authentication mechanisms, and insecure data storage. Application scanning tools simulate attacks to identify weaknesses that could be exploited by malicious actors. By performing regular application scans, organizations can identify and address vulnerabilities in their applications, reducing the risk of compromise and data breaches.
Database Scan
Database scanning involves assessing the security of databases, such as relational databases (e.g., MySQL, Oracle) or NoSQL databases (e.g., MongoDB, Cassandra). The scanning tools examine the database configuration, access controls, and user privileges to identify vulnerabilities that could lead to unauthorized data access or manipulation. Database scans check for misconfigurations, weak passwords, lack of encryption, and other vulnerabilities that could compromise the confidentiality and integrity of stored data. Regular database scanning helps organizations protect sensitive data and ensure compliance with data protection regulations.
Host-based Scan
Host-based scanning focuses on identifying vulnerabilities in individual systems, servers, or endpoints. It involves scanning the operating system, installed software, system configurations, and other components of the host for known vulnerabilities. The scanning tools compare the system configuration against a database of known vulnerabilities and security patches to identify potential weaknesses. Host-based scans help organizations identify vulnerabilities that could be exploited by attackers to gain unauthorized access, install malware, or compromise the system. Regular host-based scanning helps ensure that systems are up to date with security patches and configurations are hardened against potential threats.
Vulnerability scanning is crucial in identifying potential vulnerabilities in different aspects of an organization’s infrastructure. Network scanning assesses vulnerabilities in network devices, application scanning focuses on web and software applications, database scanning examines database security, and host-based scanning identifies vulnerabilities in individual systems. By conducting regular vulnerability scans, organizations can proactively identify and address security weaknesses, reducing the risk of exploitation and improving their overall security posture.
